
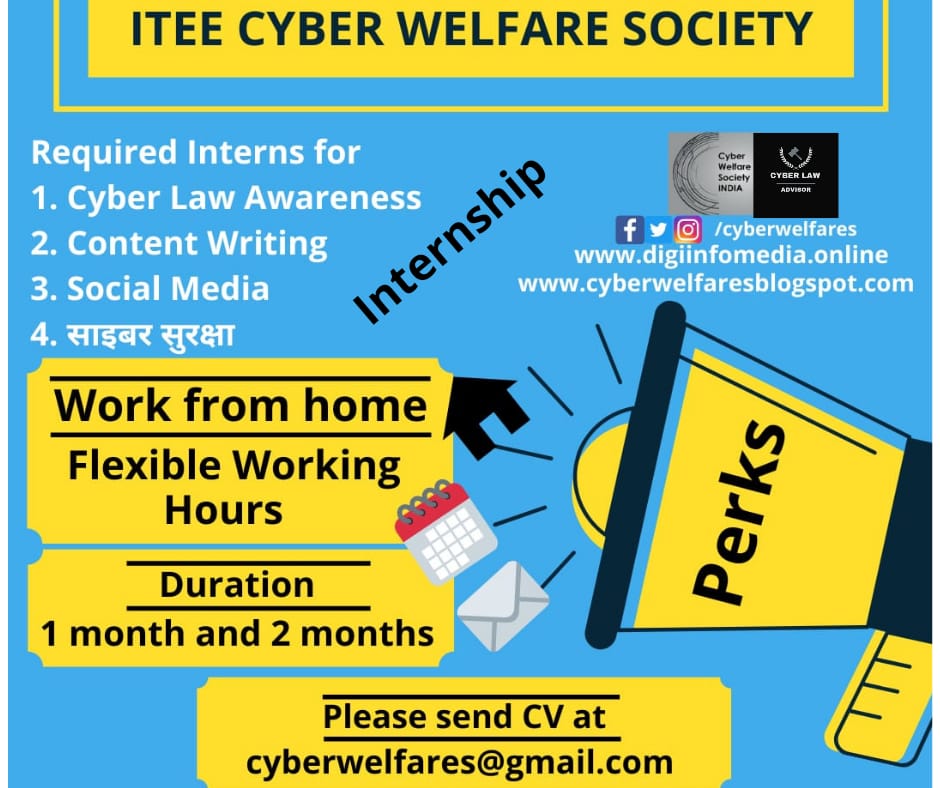
We Are Organising A Cyber Welfare Internship Programme for minimum of 30 days and maximum 90 days. During The Internship Students Will Gain Complete Knowledge About Cyber Law and It’s Different Aspects. During the Internship Each And Every Candidate Will Have To Write Article On Cyber Law And Cyber Security Awareness. Under Which Selected Articles Will Be Published On Our Portal As Well As On Different News Portal .As We Know Now A Days Many People Are Facing Problems Regarding Cyber Crimes That’s Why We Tend To Aware More And More People About The Cyber Awareness Through This Internship Programme. Our Organization Was Started In 2016 And Also It Is The First Cyber Welfare Society Of India.
Terms and conditions-
1. Stipend unpaid.
2. Candidates must be punctual and must have an active participation in the working and other activities.
3. The candidate must be enthusiastic in learning, good communication skills.
4. The final selection procedure will be based on your answers to the questionnaire and the telephonic interview. The interview will take place after the introspection of your answers.
5. Certificates will be provided after the termination of the internship.
https://cyberwelfares.blogspot.com
Email answer’s to
cyberwelfares@gmail.com
Selected intern’s day-to-day responsibilities include:-
1. Writing about cybersecurity and cybercrime law
2. Learning internet law and communicate with the people about cyber law
3. Making people aware of cyber law and cyber security
4. Conducting social media marketing for the NGO to make people aware of cybersecurity and cyber-crime law
5. Writing about cyber-crime fraud and help cyber-crime victim.
*CYBER Security awareness survey*
Questionnaire :
Q1. Give your views in not more than 200-250 words about any of the following topics : ( OWN VIEWS NO PLAGARISIM )
a. Cyber Crime Scenario in India
b. Cyber Forensics
c. Mobile Forensics
d. Scenario of Cyber Law in India
e. Mobile Apps – Are they threat to Data Privacy
Q2. Why are you interested in doing internship in Cyber Welfare Society.
Q3. How do you justify your interest as per you qualifications into Content writer.
Q4. Have you done anything or doing currently to prove your interest in the field of Cyber Crime/Security.
Q5. Give your reflection about Various CyberCrimes and how can we protect.
Social media Presence –
http://www.facebook.com/cyberwelfares
Cyber Welfare Society Facebook
http://www.instagram.com/cyberwelfares
Cyber Welfare Society Instagram
Email answer’s to
cyberwelfares@gmail.com





A)The cyber crime was most un wantedly ised in india
B) The cyber forensics an attacker can be identified by clue(ip address or something clue)
C)the mobile forensics it can be some one watching your data(google) ex: online shopping ads
D) the cyber security law was can not be affect the attacker in india because punishment was very less so attacker easly escape to the case
E) A some mobile application collect the user data and injuct tje threats and virus. ex:uc,super clener
2) i amvery much to intersted to cyber security because avoid data piracy.
3)my qualification how to avoid threat and malware on mobile phone and remove the virus to write a content to other people
4)yes. I can be break any kind of wifi and create the small antivirus
5)the user can be mostly used in open source os and open source app to avoid the cyber crimes ex:linux(os),firefox(browser)
1. Mobile Apps are a serious threat to our Data Privacy as many people do not read the privacy policies and clicks on I agree without knowing that what information of the user the App is going to use and up to which extent it is going to be used. Also, many apps such as Paytm etc which are directly connected with our banks can be hacked which can lead to financial loss as well as getting our precious financial and personal information in wrong hands.
2. As I am a Cyber Law student and in order to explore more about cyber Law and learn more about the domain I am more interested in this internship.
3. Being a law student I should be capable enough to do research work and write about the present scenario.
4. I have written one research paper and one Essay and also have organized many techno-Legal moot courts for the same.
5. There are many kinds of Cyber Cyber Crimes such as E-Commerce frauds, Banking Frauds, Crimes including Cyber Stalking, etc which can be prevented only if we are aware of the crimes and it’s preventing measures.
Home Video Business Technology News Media Cyber Security Featured Contact Us
ITEE CYBER WELFARE SOCIETY INDIA.
ITEE CYBER WELFARE SOCIETY INDIA.
AdminJune 26, 2019
FacebookWhatsAppTwitterEmailShare
Hello Readers,
Greetings from ITEE Cyber Welfare Society
We Are Organising A Cyber Welfare Internship Programme for minimum of 30 days and maximum 90 days. During The Internship Students Will Gain Complete Knowledge About Cyber Law and It’s Different Aspects. During the Internship Each And Every Candidate Will Have To Write Article On Cyber Law And Cyber Security Awareness. Under Which Selected Articles Will Be Published On Our Portal As Well As On Different News Portal .As We Know Now A Days Many People Are Facing Problems Regarding Cyber Crimes That’s Why We Tend To Aware More And More People About The Cyber Awareness Through This Internship Programme. Our Organization Was Started In 2016 And Also It Is The First Cyber Welfare Society Of India.
Terms and conditions-
1. Stipend unpaid.
2. Candidates must be punctual and must have an active participation in the working and other activities.
3. The candidate must be enthusiastic in learning, good communication skills.
4. The final selection procedure will be based on your answers to the questionnaire and the telephonic interview. The interview will take place after the introspection of your answers.
5. Certificates will be provided after the termination of the internship.
https://www.cybercrimemedia.com/2019/05/internship-for-students.html?m=1
Email answer’s to
cyberwelfares@gmail.com
Selected intern’s day-to-day responsibilities include:-
1. Writing about cybersecurity and cybercrime law
2. Learning internet law and communicate with the people about cyber law
3. Making people aware of cyber law and cyber security
4. Conducting social media marketing for the NGO to make people aware of cybersecurity and cyber-crime law
5. Writing about cyber-crime fraud and help cyber-crime victim.
Cyber Awareness Survey-
*CYBER Security awareness survey*
https://docs.google.com/forms/d/e/1FAIpQLSeHNlTvxg2cY9KLI4vxNESK-lqdC4iO8htxvOP79wcHu_mQUw/viewform?usp=sf_link
Awareness Survey
Questionnaire :
Q1. Give your views in not more than 200-250 words about any of the following topics : ( OWN VIEWS NO PLAGARISIM )
a. Cyber Crime Scenario in India
b. Cyber Forensics
c. Mobile Forensics
d. Scenario of Cyber Law in India
e. Mobile Apps – Are they threat to Data Privacy
Q2. Why are you interested in doing internship in Cyber Welfare Society.
Q3. How do you justify your interest as per you qualifications into Content writer.
Q4. Have you done anything or doing currently to prove your interest in the field of Cyber Crime/Security.
Q5. Give your reflection about Various CyberCrimes and how can we protect.
Social media Presence –
Cyber welfare society Twitter
http://www.facebook.com/cyberwelfares
Cyber Welfare Society Facebook
http://www.instagram.com/cyberwelfares
Cyber Welfare Society Instagram
Email answer’s to
cyberwelfares@gmail.com
FacebookWhatsAppTwitterEmailShare
Avinankudi Murugesan
June 26, 2019 at 4:45 pm
A)The cyber crime was most un wantedly ised in india
B) The cyber forensics an attacker can be identified by clue(ip address or something clue)
C)the mobile forensics it can be some one watching your data(google) ex: online shopping ads
D) the cyber security law was can not be affect the attacker in india because punishment was very less so attacker easly escape to the case
E) A some mobile application collect the user data and injuct tje threats and virus. ex:uc,super clener
2) i amvery much to intersted to cyber security because avoid data piracy.
3)my qualification how to avoid threat and malware on mobile phone and remove the virus to write a content to other people
4)yes. I can be break any kind of wifi and create the small antivirus
5)the user can be mostly used in open source os and open source app to avoid the cyber crimes ex:linux(os),firefox(browser)
Reply
Divya Samriti
July 9, 2019 at 2:10 pm
1. Mobile Apps are a serious threat to our Data Privacy as many people do not read the privacy policies and clicks on I agree without knowing that what information of the user the App is going to use and up to which extent it is going to be used. Also, many apps such as Paytm etc which are directly connected with our banks can be hacked which can lead to financial loss as well as getting our precious financial and personal information in wrong hands.
2. As I am a Cyber Law student and in order to explore more about cyber Law and learn more about the domain I am more interested in this internship.
3. Being a law student I should be capable enough to do research work and write about the present scenario.
4. I have written one research paper and one Essay and also have organized many techno-Legal moot courts for the same.
5. There are many kinds of Cyber Cyber Crimes such as E-Commerce frauds, Banking Frauds, Crimes including Cyber Stalking, etc which can be prevented only if we are aware of the crimes and it’s preventing measures.
Currently the world is going through technology and information based era . And India also the part of digitalization era but here some demerits of this digitalization in criminal activities which is called cyber crime . Cyber crime scenario in India every people effects cyber crime . India is second highest user of internet and users increases rapidly and rural population are more effected.
Cyber forensics means to investigate the cyber crime , finding the unseen facts behind the crime . Investigating with the help of software , hardware and network tools for tracing location and criminals .
Mobile forensics also a part of cyber forensics . With the help of mobile forensics easy to find out criminal activities with the help of searching and surfing history , easy to recover data and easy to find its location and other type of information .
Cyber law also called as internet law that involves the legal issues related to the use of internet and regulation of cyber space .Cyber law in India are incorporated in the Information Technology Act ,2000 and IT amendment act 2008.
Mobile apps , In our IT act no specific rule and regulations regarding mobile applications . All mobile applications access the users private information and sold out to marketing companies . Data breach and data theft are doing by the mobile applications , yes they are threats of data privacy .
I love to be a part of welfare society working in cyber law , cyber security and cyber awareness programs .
I am doing Post graduation diploma in cyber law and I want to be a work in this field because cyber crime is major issues every develop country suffer cyber attacks and cyber crime .So need to aware people .
In the income of cyber crime is 70% . Cyber crime give more profit to IT companies comparison other services . Various cyber crime like hacking , viruses , pornography, money laundering , online gambling , cyber fruad and cheating , cyber defamation , cyber terrorism and cyber attacks , ramsomware, ATM fraud , carding , data theft , E- Theft , social engineering , social media platform , bullying , stalking ,phishing , piracy , domain name disputes ,copyright issues , trademark etc many more types of cyber crimes
Protection against cyber crime is only knowledge and awareness , never trust in online , never share personal information , always use antivirus and update your system , never click on unknown link and websites , never download unknown files . Online safety and security is awareness , And to more amendment in IT act -2000 and more strictly follow the cyber law .
Currently the world is going through the digital era every thing is going digital it makes our work easier as it is convienience for all to use it in minutes and seconds we get all the information easily on internet it ahs several merits but also demerits some people aare makin misuseoff the digitalization and performing criminal activities which is called cyber crime in the cyber world .cyber crime scenario in india is the most of the people are effected by it and it gives personal as well as monetary loss to the person.India is country which is highest user of the internet. The crimes which are commited now a days there is some where role of the cyber world like moblies computers etc
Cyber forenensic means the investigation of the cyber crimes which are done by the person these cyber crimes are done through the computer and mobile phones the highest cyber crime is of hacking childpronography financial fraud crimes etc hacking is crime which is mostly done where the the personal data of person is hacked by the hacker without his knowledge and make the misuse of them the financial fraud crimes in mosy done in now a days by sending a messagesand emails of lottery and demanding there banking information to send the lottery money and people are sharing there information which later affect the monetary loss to them.
Cybercrime can be difined as offence that are commited through the internet individual or group of induviduals the harms the reptation of a victim and causes the physical and the mental loss.
I am law graduate student and i have taken a subject of cyber crime in my last year.i have a knowledge of cyber world and the cybercrimes
Being a law student i am capable to do enough research on it and the current scenario now a days.
2. The answers to these questions are difficult to determine as it depends on the severity of the incident. With regards to the first question, the role of forensics becomes significant. The evidence collected from the crime scene is carefully examined to understand the “who, what, where, and why” of the incident. Cyber forensic investigators make detailed reports of the incident to solve all queries and to use the collected information to prevent similar attacks from occurring in the future.
The term forensics, in its literal sense, stands for an established scientific process to collect, analyze, and present evidence collected from an investigation. The difference between a crime and cybercrime is that, when a cyber attack happens, the evidence is usually found in digital devices.
Cyber forensics also includes being able to present the findings in a way that is accepted in the court of law. The aim of digital forensics is to preserve evidence in its most original form so that a structured investigation can be performed to reconstruct past events.
As cybercrime increases, there is a strong need for cyber forensic expertise in all business models and more importantly among law enforcement agencies who rely on computer forensics to find cyber criminals.
Cyber Forensics—Tools and Tasking
Cyber forensic investigators are experts in investigating encrypted data using various types of software and tools. There are many upcoming techniques that investigators use depending on the type of cybercrime they are dealing with. The tasks for cyber investigators include recovering deleted files, cracking passwords, and finding the source of the security breach. Once collected, the evidence is then stored and translated to make it presentable before the court of law or for police to further examine.
Many believe that recovering false data is the key objective of cyber forensics. Though the creation of this science was meant to investigate false data, the enhancement of new techniques has added a larger scope through cyber forensics. The science of cyber forensics dates back to the era of floppy discs and since then it has evolved, growing parallelly in complexity with cybercrime.
Cold cases and cyber forensics
Cold cases stand for the type of cases that were not solved and left pending due to the lack of actual evidence. Law enforcement agencies are now reopening unsolved cold cases so that proper evidence can be gathered using cyber forensic methodologies.
Cold case of BTK solved after 13 years with the help of cyber forensic [1]
Between 1974 and 1991, BTK (bind, torture, kill) strangled 10 people and this was a mystery to the Wichita, Kansas police and FBI. BTK performed the acts out of bizarre fantasies by inflicting pain on his many victims, of whom two were children, 9 and 11 years old. The local police and FBI interrogated countless people, collected 1300 DNA samples, and analyzed his depraved writings that he used to send to local media along with puzzles and pictures. But all the efforts of law enforcement were in vain, and caused the case to go cold.
After 13 years, when BTK resumed communication with police and sent a message on a floppy disk, computer forensic experts analyzed the floppy disk for information and recovered a word document. The experts also retrieved metadata which is nothing but information about data where they found the name in the last modified file “Dennis” and the phrase “Christ Lutheran Church.” When searched online, on the website of the Lutheran church, Dennis Rader appeared as a president of the congregation council. The police initiated surveillance and a collected DNA sample from his daughter that proved that Dennis Rader was a criminal. He was then arrested in February 2005 and pled guilty. He was sentenced to 10 consecutive life sentences for his crimes.
Role of Cyber Forensics in Crime
The role of cyber forensics in criminal investigations is constantly increasing because of the skill that is required to retrieve information and use it as evidence. Though this task appears to be difficult for cyber forensic investigators, this is their expertise. Therefore, the demand for skilled professional is also growing. In the year 2015, Forbes Magazine declared the cyber forensic investigation as a number one profession [2]. It is not just a critical position but the one that supports law enforcement by helping in solving the cases and impacting the overall efficiency of the team.
“Cyber crime scenario in India”
The condition in India right now about the use of Social media is not good because people are not aware of their limitations over social media, All they guess from the self is that they can do anything on social media platforms and no one is here to stop them and reason behind this thinking might be low grasp over accused of cyber crimes.
The situation can be improved by making a separate law for Cyber crime as right now IT act of 2000 is applicable on all these matters and it have many loopholes that can be improved by making a new law.
I am free in june month
I Am available for june month
Cyber crime is one of the most common threat followed in India. People using social media without being aware of the terms and policies and just make an account by clicking on “I agree to terms and condition” without going through them. This should be stop and people must be aware of all this cyber law and internet law..and they should know the options that are available to them if cyber crime is committed by them or for them.
1.Cyber crime is one of the most common threat followed in India. People using social media without being aware of the terms and policies and just make an account by clicking on “I agree to terms and condition” without going through them. This should be stop and people must be aware of all this cyber law and internet law..and they should know the options that are available to them if cyber crime is committed by them or for them.
2.As a law student it would be a great opportunity for me to do internship for the awareness of cyber crime and cyber law…even it was our subject, which we have studied so it would be helpfull for me as well as for others.
3.It would be easier for me to define and write the article on cyber crime and cyber law, as i am a law student and it was a part of our studies.
4.No, but i am interested to do so.
5.Cyber crime can be done against anyone. It can be against an individual or the government or it can be against the society or any company….For protecting yourself and your things from cybercrime use stong password which contain upperclass and lowerclass letters and special letters and numerical values, Back-up your important data, Do not agree to the terms and conditions without reading it, use your own internet instead of public wifi.
1.on to the date every mobile app are in the mind to make money so they allow advertisement to run on our mobile application. That the third part advertisement may be big threat for data in the mobile and most of mobile application requires a access of our phone camera,photos and other datas but the reliability of the application is big question
Mark.
2.as I have studied computer science in 12th standard. That makes me to get interest in cyber security.
3.by the following tasks u will justify. Y interest on content Writing
4.i have not done anything yet,but I get a chance I wil prove it.
5.Most of the virus attack in mobile are due to downloading the application using third part website or software. To prevent this download only the application verified by google play store or apple store etc
Q1
A)India is no doubt to imposing sanctions for deal with such crimes. The situation today is that there are several laws protect cybercime each one having it’s own scope and limitations in india.
B) cyber forensics :is an electronic discovery technique used to determine and reveal technical criminal evidence. Although still some tools can be used to investigate the evolving attacks of cyber forensics
C) mobile forensics:is a branch of digital forensics and it is about the acquisition and the analysis of mobile devices to recover digital evidence of investigative interest.
D) scenario of cyber law in india:In india most of cyber crime cases are committed by educated person. So it is required the deep knowledge and prevention. Also in india most of the cases found where crimes are committed due to lack of knowledge or by mistake. So be give some welfare to all by creating awareness.
E) Mobile apps are they threat to data privacy:Mobile apps security threats includes everything from mobile forms of malware and spyware to the potential for unauthorized access to a device’s data.
2)Some of them don’t know about cyber crime. Even though they indifference their detail in public place. So i want to create some awareness about cyber cimes. So think this the right way to do my work
3)i’m an computer science student .I’m interested on hacking and break wifi passwords but laterly i realize this crime is very illegal thing some of them don’t know about it that is the chance to easily hack others devices. Inbetween thing their personal will be leaked by a small way. So i want take some action against hackers and crimers. So i want to create some welfare for all the people
4)yes,i have done one presentation in last year for cyber security and also i explained my friends about cyber crimes and how to protect our device from crimes.
5)Don’t repeat the passwords on different sites, and change the passwords regularly. Make them complex. That means using a combination of at least 10 letters, numbers, and symbols. A password management application can help to keep the passwords locked down.manage the social media settings and you should only handle your device don’t give it to anyothers.
Our is becoming digital day by day but cyber crimes is also increasing day by day. In cyber field there is lots of crime like phishing, making clones of device, doing hacking to improve there knowledge etc. We have to be updated. In college and in university have many courses on cyber security law. Students can take information and our society aware.
As i have read all the articles provided above i came to acknowledge a feedback that it provides so much information about different types of cyber crimes occurring round the world and also the legal securities or law provided for help to stop such heinous crime. Also case studies are included with so many sections. The youth and women of our society are the most easiest prey or victims to this. Lastly it also provides that how a Cyber Welfare Society in Indore wants to help such affected victims and crimes over the years are also provided which helps us to gain knowledge and also helps to learn from the past mistakes committed by people.
I Chinmoyee Sur, an under-graduate student of Bhawanipur College, Kolkata want to join and contribute in this welfare society fully at my own interest to know more knowledge about this cyber crime and its securities, helping all my peers in this evolving issue and take a pledge to spread knowledge and skills about all the laws, sections, acts and other safety measures of this domain through speaking sharing and providing a helping hand to all and to reach out a mass out there.
1.If we talk about india cyber crime is one of the crime which is being followed for girls to threaten them. The problem these thing happen is that people are not aware about the terms and conditions of social media app , because they just want use the app so they just press the button ‘I agree’ . In India people won’t use this platform(social media) for good they just use it for there satisfaction and some of them commit crimes.People are not much aware about cyber crimes and laws related to it. Now a days teenegers and people above the age of 50 were more using these platform and they usually don’t understand any malicious activity happening to there social media account.
2.As I am law student it would be great for me. The internship will be useful for me as I have to study it in future. And now a days it’s important for everyone that they should at least know a basic of these crime so if it happen with me or anyone else they can take action against it.
3. As a student it would be easy for me to do reasearch work for upcoming time and it will help for writing an article or a report work.
4. No, but know i thinks it’s a great opportunity for me to do so.
5. It can be against anyone. Against individual or against any group of people. For protecting it People should use the apps after reading all the terms and conditions. You should provide a strong password (using special symbols) and should not share it with anyone. Most important if you are using any app where there is two factor verification on this option it will help you from unauthorized access to your account. At last don’t click on the links which are not authorized or may have some threats.
2) I am interested in doing internship at Cyber welfare society. I am very much curios to know more about cyber law and research about it. And I would also like to make people aware about whatever I learn or research through my articles.
3) I have to be honest, my qualifications are basic, nothing fancy. But I am very much interested in Cyber law and Cyber crime. I have not written articles on these topics but yes as an English hons. Student, I am good with words and how to convey my emotions and expressions.
4)I haven’t done anything or doing currently which involves these topics.
5) There are so many fields in cyber crime that whenever we say these two words cybercrime in front of people, they all have different answers to it, some say hacking, some say phising, some say catfishing. If we look at the wider version of cyber crime, all our information and personal data is being backed up in our phones and memory cards, that it makes people to tap into these faster. But this is a cyber crime. We can prevent it by not telling unknown callers our personal information or save our private information in public accessible sites or wherever.
1. A) The cyber crime scenario in our country does not truly reflect the existing situation on the ground but COVID 19 situation cyber crime is on high because all people do the work form home so all the data is transferred through internet and cyber crime was most unwanted issue in india.B) The process of gathering and documenting proof from a computer or a computing device in a form presentable to the court by applying the techniques of investigation and analysis is called Cyber Forensics. Cyber Forensics is also called Computer Forensics. The aim of cyber forensics is to determine who is responsible for what exactly happened on the computer while documenting the evidence and performing a proper investigation. .C) Crimes do not happen in isolation from technological tendencies; therefore, mobile device forensics has become a significant part of digital forensics.Mobile apps are serious threat to or data privacyD) Cyber crimes can involve criminal activities that are traditional in nature, such as theft, fraud, forgery, defamation and mischief, all of which are subject to the Indian Penal Code. The abuse of computers has also given birth to a gamut of new age crimes that are addressed by the Information Technology Act, 2000.E) Mobile apps, in our IT act no specific rule and regulation regarding mobile application. All the mobile application access the users private information and sold out to marketing companies. data breach and data theft are doing by the mobile application , yes they are threats of data privacy.2) Yes , i m interseted in doing internship in cyber welfare society because i love to be a part of welfare society working in cyber law and I gain a knowlege of cyber law, cyber security and cyber awareness programs.3) Being a law student I should be a capable to do enough research on present scenario.4) No, but i want to do internship under you because i want to gain knowlege about cyber crime and i decided that i make my carrer in the filed of cyber crime so, started work on my goal recently And i hope you give me a chance to do internship under you.5)When any crime is committed over the Internet it is referred to as a cyber crime. There are many types of cyber crimes and the most common ones are, Hacking, Theft, Identity Theft, Cyber Stalking, Malicious Software,Child soliciting and Abuse.#some ways that we protect overself from cyber crime are given below:-1. Keep your software updated
2. Protect ourselves against identity theft.3. Use strong password.4. Use diffrent passwords from diffrent sites5. Dont share your One Time Password (OTP) with unkown one.6.Don’t bank on public wi-fi7.Use anti-virus software
8. Don’t store your card details on websites
9.Lock down your FB account10. Ignore pop-ups
1.to talk about cyber crimes we till now come haveacross various cyber crimes such as frauds,thefts, terrorism and for the sole purpose IT act came in force on 17oct,2000 to prove efficacy but in our country along wid rise in digitalisation ,india is becoming epic centre of cyber crimes wid more than 10k cases per year .we witness various crimes such as virusattack(43c), unauthorised access(43a), DOS(43f),data theft, phishing (419ipc,66D)of IT, cyber terrorism, stalking , unethical hackking,spaming and much more .To tackle wid this issue govt is taking various laws nd measures,entering treaties and also cyber cells of crimes investigation dept is brainchild of this to curb the crimes ! 2. M law student and done basic diploma course in cyber law which further arouse my interests and felt it very useful in daily life so further want to learn more.3.being law Student I should have knowledge of all this tech related crimes and this can help me in my later career also to do research work 4..yes I hv done diploma in cyber law though don’t have any experience related to it but further Hoping to gain knowledge and experience 5.hacking, terrorism, spoofing, spamming,stalking,breach of privacy, trafficking of computer system, squatting,xss, and. Alot along with IT and IPC provisions various rules and regulations have been passed! only strict implementation will be proved fruitful and also internet users especially youths should take lot of precautions be4 exposure of any private info ,making payments widout checking out the sites ,we should not click any link attachments through our mails also downloading anti virus app will help to detect virus .
e. most people believe that data privacy is an important issue. In some manner, we need privacy or ensure that some information like financial, permanent address should not be a piece of open information but other than that I also think that when a company takes some of your information its mostly because that want to sell us some product or service and make a personalized advertisement, which can be a great tool for a person who is trying to find some product or service. we do have to make sure as a buyer that we do not fall for any scam or inferior quality item.
when the GPS feature came it scared many people that anyone can track your cellphone and that we were not safe but it helps us track our lost phone and even help to catch bad guys. Every item can be used in the wrong ways but it all depends on the user and knowledge of the buyer.
Q2 I am a first-year law student at a national law university and still exploring different fields of law
Every thing possible just because everyone one set the goals, remove the activities and without knowing not open the ant links rather that is stop this problem and some salutations.
1.Cyber crime scenario in India increase rapidly. In our India there are so many cases related to cyber crime like credit card fraud, misusing of website through hacking and so on. Now a days, people work from home they are using there data at home without any safety because of this some people misuse there data and start doing crime. So,. In my opinion data hacking is a big issue in cyber crime
2. I am interested in this internship because I am very curious to know more about cyber crime I have interest in this field that how’s it work and how we can solve our cases if we have.
3. I love to do research work if I research the topic I am able to explain and I think I can write more more relevant points in the content.
4. Yes, In lockdown I am attending some webinar related to cyber crime.
1.
a) As India is marching towards being a more digitalized state , the country is susceptible to more and more cyber crimes than ever before. The number of cases of cybercrimes have rapidly increased since more people are on the internet. People need to be made aware of the various threats on the internet and also how to avoid them.
b) Cyber forensics is the analysis of online accounts and digital accessories with on objective to find digital evidences . This process includes examination of chat messages, call history, files shared ,location details , various online accounts etc.
c) Mobile forensics is a part of the cyber forensics investigation where the contents and settings of mobile phone is examined in search for relevant information regarding a case. As mobile phone have become a standard living accessory , mostly the vital information for the case is found in the smartphone itself.
d) The cyber law in India under the IT acts deal with various online malicious activities such as
fraud ,harassment ,stalking ,defamation ,impersonation etc. Even though there are suitable laws for cyber crime in India ,people generally don’t report cases and even if they do , the tracking and tracing of these criminal offences is far less effective than other countries due to less available workforce and resources.
e) People do not verify the sources of the apps and even if they do , they fail to go through the privacy policies and the permissions they allow those apps to use which lead to a major threat to privacy.
2. After diving deep in the field of cyber security , I observed how vulnerable we all are in this digital era, so I decided to spread the awareness among people so that they can protect themselves and lead a better and safe life. I am interested in Cyber Welfare Society as I want to reach out to more and more people to tell them how to lead a healthy digital life devoid of worries.
3. I have attended many trainings in the field of cybersecurity and am experienced in practical as well . I am aware of the various techniques in which someone can be compromised as well as how we can make oneself safe .The main thing that justifies my position as the content writer is the practical knowledge on the topics along with the theory.
4. Currently I along with some of my friends am working on various projects related to social media and search engines etc.
5.There are various types of cybercrimes such as phishing ,spamming ,identity theft, online scams etc. All of these have a devastating effect on the individual or companies activities on various scales. These types of crimes can be prevented by following a set of rules In our day to day life like
i) not opening unknown emails, links ,websites etc
ii)not sharing personally identifiable information on social media
iii)reporting any malicious activity as soon as you notice it in your accounts or profiles
iv)keeping secure passwords and regularly updating them